
WHOIS records have long been used in cybercrime investigations to provide starting points in identifying perpetrators. What many may not know is that historical WHOIS records provided by products like https://iqwhois.com/whois-domain-history also serves many cybersecurity uses that we’ll discuss in more detail in the following sections.
Table of Contents
Threat Contextualization
WHOIS history can provide context behind threat data obtained from security systems. Incorporating a historical WHOIS record database into a security system, for instance, can help cybersecurity investigators contextualize security alerts by looking into past connections to other indicators of compromise (IoCs) and known threat actors.
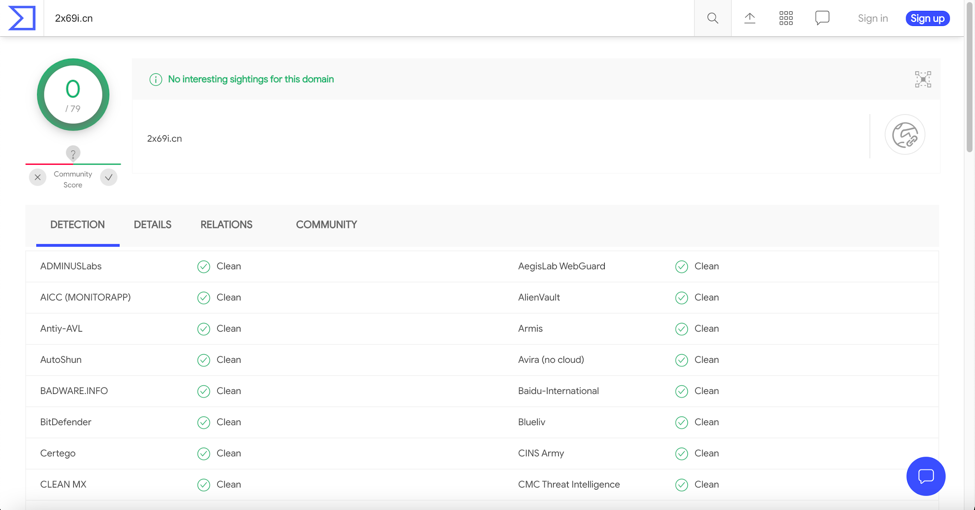
Take the domain 2x69i[.]cn as an example. A check on VirusTotal, an open-source threat intelligence source used by many cybersecurity experts, showed that it has no known malicious ties.
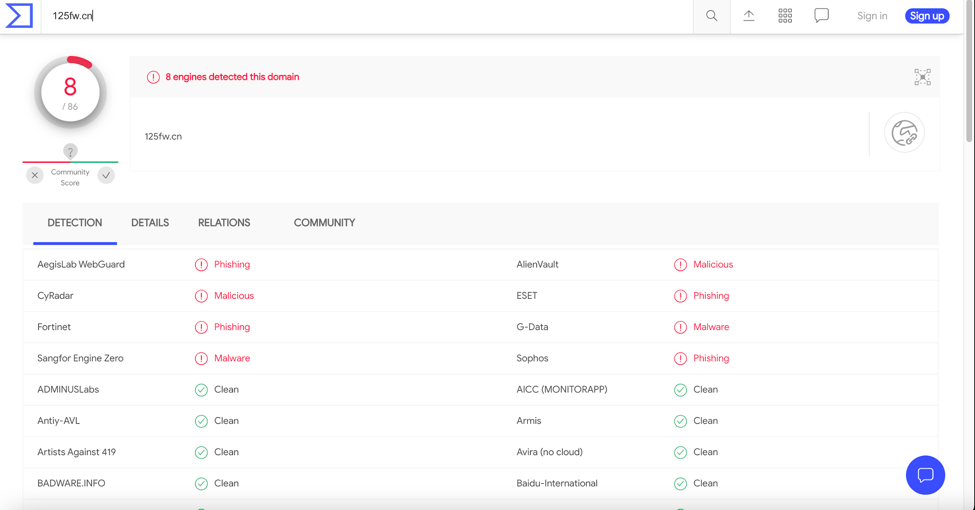
But by scrutinizing the domain’s history, you would find out that its registrant email address *****85938@*q[.]com has ties to 357 other domain names, some of which (e.g., 0jx9me[.]cn [cited for phishing], 01jope[.]cn [cited for malware distribution and phishing], and 125fw[.]cn [cited for malware distribution and phishing]) were dubbed “malicious” by VirusTotal. There could be others, of course, but this illustration showed that while 2x69i[.]cn may not be considered dangerous, its potential owner (i.e., the one who owns its registrant email address) may not be worth trusting.
Avoiding Associations with Age-Old Threats and Known Cybercriminals
Choosing the perfect domain name for your business is hard. It’s even more challenging if you wish to avoid using a domain that has had ties to malicious activity.
One way to ensure the domain name you choose for your business’s home isn’t blocked on any network or blacklisted is by researching its WHOIS history. Only by looking into every single record throughout its existence can you be sure it is threat-free.
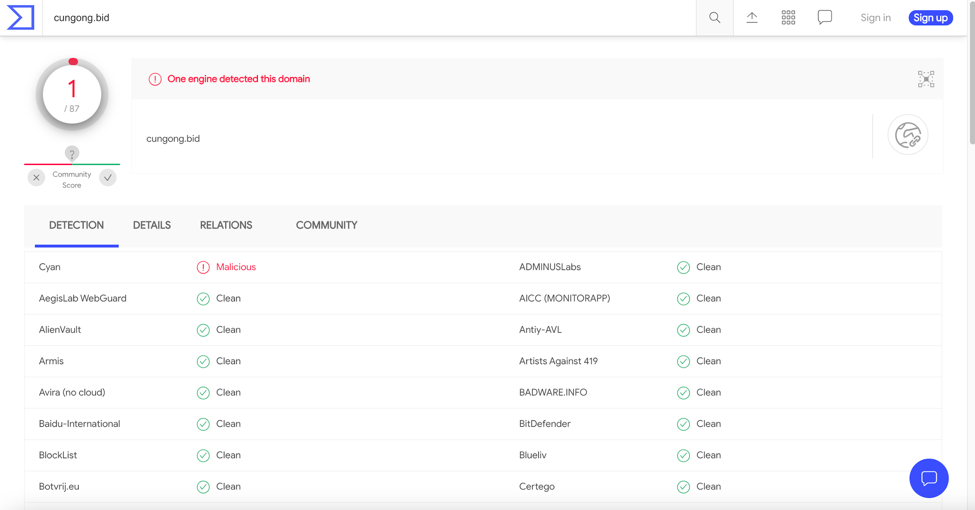
You can start your domain ownership history research by scouring through the FBI’s Most Wanted Cyber list. Looking closely at Zhang Haoran or “Black Alex,” “Metasploit,” or “EvilC0de,” for instance, using his name as a WHOIS history search term would give you a list of 142 domains. That list would include the domain names cungong[.]bid and zzzhaoran[.]top, which are categorized as “malicious” by VirusTotal.
See a Cybercrime Investigation through Despite WHOIS Redaction
Since data privacy laws like the General Data Protection Regulation (GDPR) were enforced, individuals and organizations worldwide began redacting personally identifiable information (PII) from their publicly accessible records, including WHOIS records. While the move does protect domain owners from spamming and unsolicited calls, it made life harder for cybersecurity investigators and law enforcers to identify who is behind an attack. WHOIS history can help with that task.
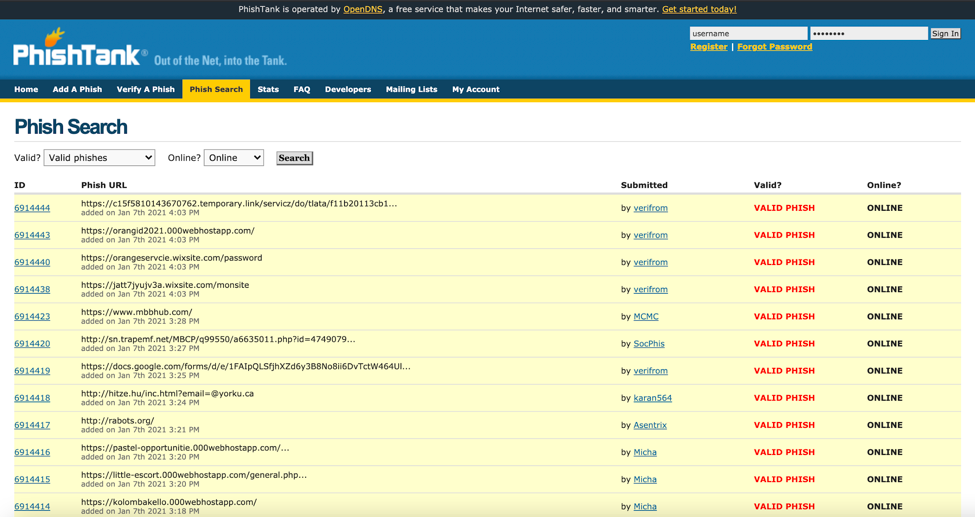
A more in-depth probe using a WHOIS history database into the domain mbbhub[.]com, a verified phishing domain on PhishTank, would show that its current WHOIS record has been redacted for privacy since 8 January 2020. But if you look at its historical WHOIS record dated 19 August 2017, you would see that an individual with the initials “P.T.” was once its owner. He may know who the current domain owner is and so could be contacted using the details he indicated in the historical WHOIS record for more information.
—
As this post showed, domain name history helps with cybersecurity requirements that include but are not limited to contextualizing threats, helping companies avoid ties to malicious activities or entities, and seeing investigations through despite privacy protection.
With WHOIS history tools’ help, cybersecurity teams can identify more potential threat sources that may not be included in published articles, security blogs, or news posts. That should bolster their organizations’ resilience to attacks. Organizations looking into acquiring new or additional domains could also benefit from accessing historical WHOIS records to ensure their pages won’t get blocked on any network. Last but not least, domain ownership history can still jumpstart any cyber investigation despite WHOIS redaction.