
For a long time, the cybersecurity community has warned companies about how newly registered domains (NRDs) can be weaponized by threat actors. Among the thousands of domains registered every day, a small percentage of them is regularly being detected as part of suspicious Internet activity.
Cases in point, we looked at some of the more recent squatting campaigns on IBM X-Force Exchange and identified additional NRD artifacts.
Table of Contents
Netflix Squatting Campaign
On 5 March 2021, Netflix users were reported to be the subject of a squatting campaign. Four domains were named indicators of compromise (IoCs)—netflex[.]tech, neflix[.]art, neflix[.]site, and netflex[.]store.
Netflex[.]tech appeared on the Domain Name System (DNS) on 15 February 2021. Neflix[.]art, neflix[.]site, and netflex[.]store, meanwhile, were all registered on 3 March 2021.
A dive into the February and March 2021 newly registered domains data feeds of https://newly-registered-domains.whoisxmlapi.com/ for .tech, .art, .site, and .store showed only 16 newly registered domains with the string “netflix,” excluding its misspelled variations. But while the volume of Netflix-related domain names with the new generic top-level domain (gTLD) extensions was small, all these could still be used in cyber attacks.
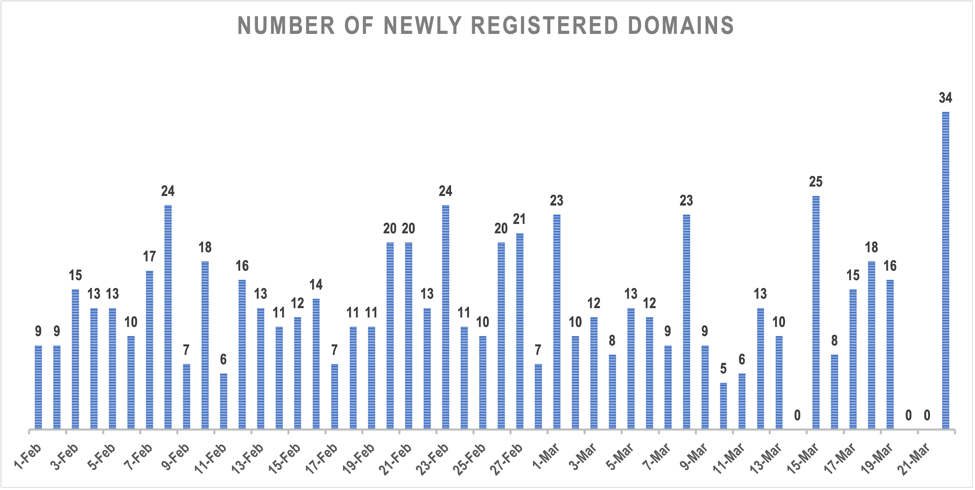
Facebook Squatting Campaign
On 3 March 2021, IBM warned users about an ongoing Facebook squatting campaign that involved 12 domains—facekoot[.]com, neofacebook[.]com, it-itfacebook[.]com, es-esfacebook[.]com, vi-vnfacebook[.]com, rajafacebook[.]com, ru-rufacebook[.]com, fr-frfacebook[.]com, ro-rofacebook[.]com, id-idfacebook[.]com, kjfacebook[.]com, and en-gbfacebook[.]com.
All 12 domain names publicized by IBM were registered on 1 March 2021, only days before the campaign was reported.
A look at the newly registered .com domain data feeds for March 2021 showed 651 newly registered domains containing the string “facebook.” This number doesn’t include misspelled variants so there could be more potential typosquatting domain names that could be used in the same or similar attacks.
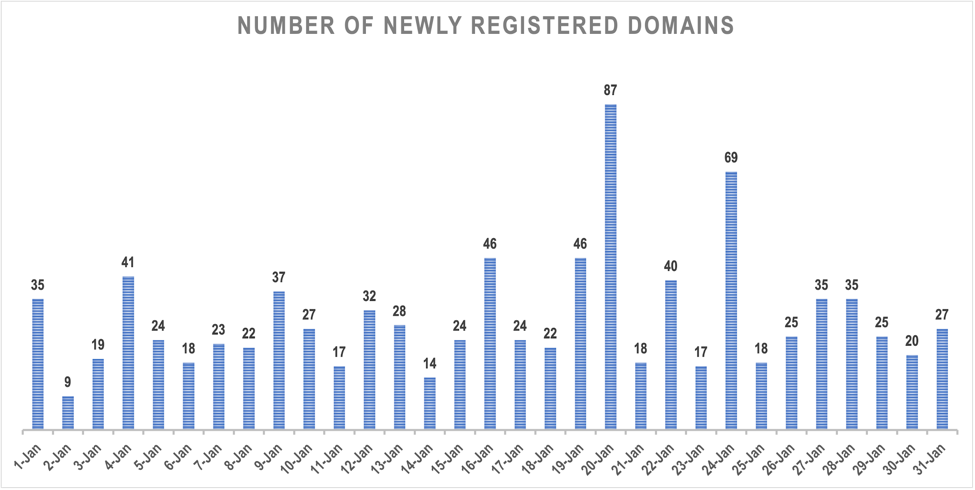
Blockchain.com Squatting Campaign
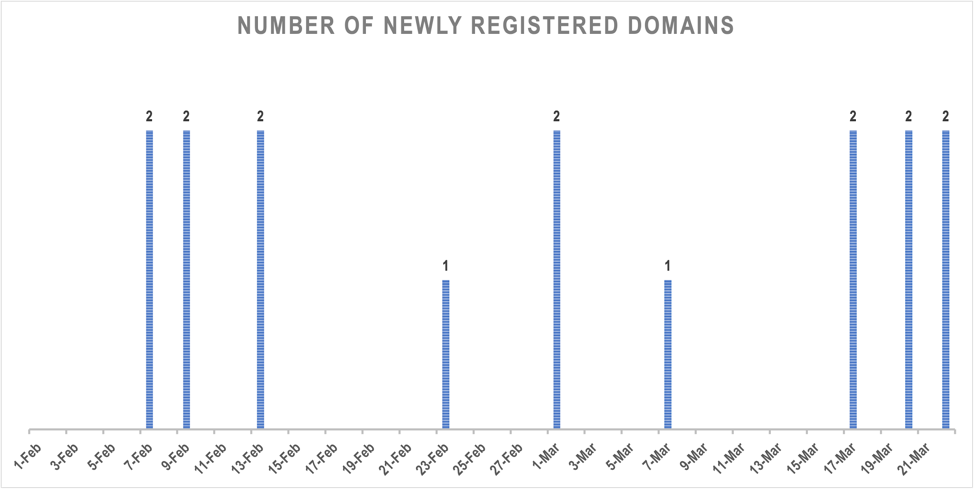
On 13 January 2021, IBM released a warning about an ongoing squatting campaign targeting Blockchain[.]com users. Four URLs were identified as IoCs—wallets-txi-blockchaln[.]com, wallets-tix-blockchaln[.]com, wallets-blokchain[.]com, and wallets-txi-blokchain[.]com.
All four domains indicated as IoCs in the IBM X-Force Exchange report appeared in the 8 January 2021 newly registered domains data feed.
A look at the newly registered .com domain data feeds for January 2021 revealed 924 newly registered domains that contain the string “blockchain.” The number doesn’t include misspelled variations of the string so there could be a lot more potential threat vectors. Any of these could figure in the campaign or other similar attacks.
General Findings
All of the domain names listed in the three IBM X-Force Exchange squatting reports were newly registered at the time they were used in the attacks. The chart below shows the amount of time in days that transpired between each domain’s registration date and when the related attack was reported or discovered.
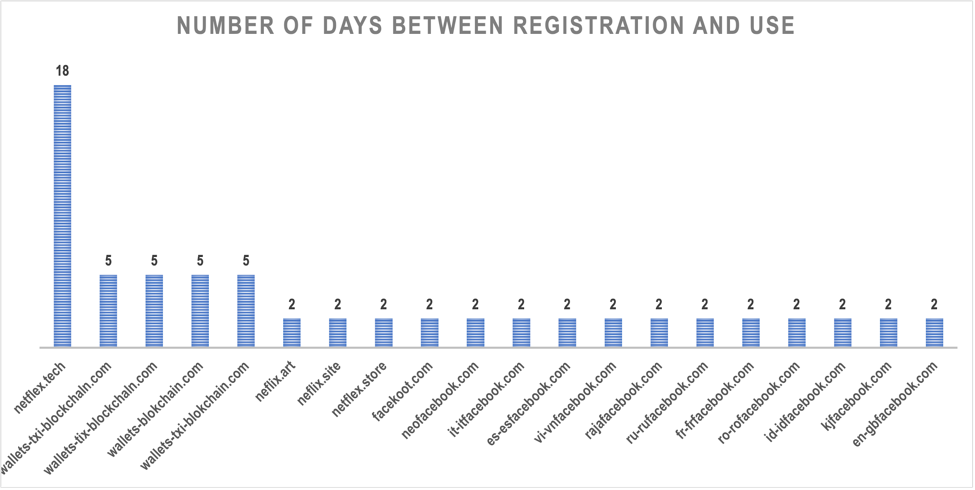
A majority of the domains (15 in all) were registered two days before they were publicized, four were up for only five days before they were used in attacks, and one was registered 18 days before it was reported.
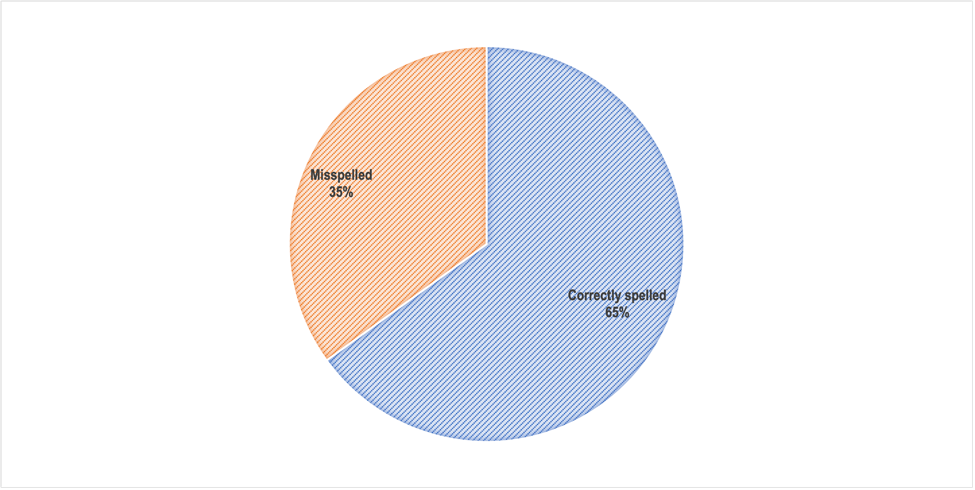
More of the IoCs were correctly than incorrectly spelled as shown below.
The more popular a TLD is (e.g., .com), the more newly registered domains use it. The domain names with new gTLDs (e.g., .tech, .art, .site, and .store) were very few in comparison to those that used .com. On average, 21 new .com domains related to threats were registered daily while only one domain sporting a new gTLD made it into the DNS per day.
Based on our analyses of three of the more recent squatting domains reported on IBM X-Force Exchange, we can conclude that threat actors indeed still use newly registered domains in their attacks.